- WHY AVERTIUM?
-
-
Why Avertium?
Context over chaos. Disconnected technologies, siloed data, and reactive processes can only get you so far. Protecting businesses in today’s threat landscape demands more than a set of security tools – it requires context.
That's where Avertium comes in
-
Considering Microsoft?
Avertium Named Microsoft Security Solutions PartnerAvertium’s managed services for Microsoft Security Solutions is delivered through the company’s premium service: Fusion MXDR. Fusion MXDR includes 24x7 monitoring and management of Defender for Endpoint and Sentinel, threat intelligence, attack surface
monitoring, and vulnerability management for Microsoft Security customers. -
Latest Avertium News
How Gartner's 2024 Cybersecurity Trends Can Guide Your Cyber EffortsGartner has identified its six top cybersecurity trends for the year, and they’re ones that healthcare leaders should consider. Of the six trends, here are the ones that Avertium finds most instructive and beneficial.
-
-
- SOLUTIONS
-
-
Governance, Risk, + Compliance
GRC with context – not complexity. -
Attack Surface Management
No more blind spots, weak links, or fire drills. -
Threat Detection + Response
Detect, adapt, and attack with context. -
Microsoft Security Solutions
End-to-end support from strategy to daily operations to maximize your Microsoft Security.
-
-
- COMPANY
-
-
About Us
Security. It’s in our DNA. It’s elemental, foundational. Something that an always-on, everything’s-IoT-connected world depends on.
Helping mid-to-enterprise organizations protect assets and manage risk is our only business. Our mission is to make our customers’ world a safer place so that they may thrive in an always-on, connected world.
-
Latest Avertium News
How Gartner's 2024 Cybersecurity Trends Can Guide Your Cyber EffortsGartner has identified its six top cybersecurity trends for the year, and they’re ones that healthcare leaders should consider. Of the six trends, here are the ones that Avertium finds most instructive and beneficial.
-
-
- PARTNERS
-
-
Our Partners
Best-in-class technology from our partners... backed by service excellence from Avertium.
-
Partner Opportunity Registration
Interested in becoming a partner?
With Avertium's deal registration, partners can efficiently and confidently connect with Avertium on opportunities to protect your deals.
-
Latest Avertium Resource
Harnessing Copilot for Security: A Strategic Approach to Healthcare Cyber DefenseMicrosoft Copilot for Security analyzes and synthesizes high volumes of security data which can help healthcare cybersecurity teams do more with less.
-
-
- NEWS & RESOURCES
-
-
News & Resources
Dive into our resource hub and explore top
cybersecurity topics along with what we do
and what we can do for you. -
Latest Resource
Harnessing Copilot for Security: A Strategic Approach to Healthcare Cyber DefenseMicrosoft Copilot for Security analyzes and synthesizes high volumes of security data which can help healthcare cybersecurity teams do more with less.
-
-
- CONTACT
Flash Notice: Windows Zero-Day Exploited - JavaScript Files Bypass Security Warnings
overview
A Windows zero-day vulnerability is allowing threat actors to use malicious stand-alone JavaScript files to bypass Mark-of-the-web security warnings. The Mark-of-the-web security feature is the Windows security warning that one sees when attempting to open a file from the Internet. Internet files can be harmful to your computer if opened from an unknown and untrusted source.
Image 1: Mark-of-the-Web Security Pop Up
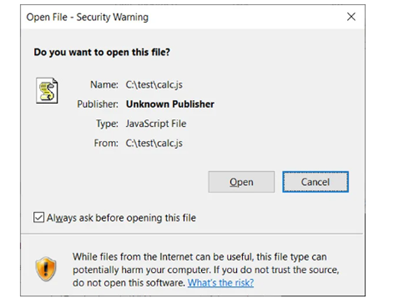
Additionally, Mark-of-the-web is utilized by Microsoft Office to determine if a file should open in Protected View, which disables macros. As of now, the security flaw does not have a CVE number or an official patch. Researchers from the HP threat intelligence team have observed threat actors infecting devices with Magniber ransomware using JavaScript files – specifically .JS files distributed as attachments or downloads that can run outside of a web browser.
After analysis, Will Dorman from ANALYGENCE discovered that the threat actors signed the JavaScript files with a malformed key. Signing with the malformed key stopped Microsoft from displaying the security warning, automatically executing the script to install the Magniber ransomware. With this technique, normal security warnings are bypassed by threat actors. Dorman believes that security flaw was present with the release of Windows 10.
The Mark-of-the-web vulnerability is concerning because threat actors have already started to exploit it in ransomware attacks. Microsoft stated that they are aware of the vulnerability and are investigating it. In the meantime, there is an unofficial micro-patch for the flaw issued by a third-party company called 0patch. The patch can be applied to the following Windows versions:
- Windows 10 v1803 and later
- Windows 7 with or without ESU
- Windows Server 2022
- Windows Server 2019
- Windows Server 2016
- Windows Server 2012
- Windows Server 2012 R2
- Windows Server 2008 R2 with or without ESU
How Avertium is Protecting Our CUSTOMERS
- Avertium offers VMaaS to provide a deeper understanding and control over organizational information security risks. If your enterprise is facing challenges with the scope, resources, or skills required to implement a vulnerability management program with your team, outsourced solutions can help you bridge the gap.
- Avertium offers user awareness training through KnowBe4. The service also includes Incident Response Table-Top exercises (IR TTX) and Core Security Document development, as well as a comprehensive new-school approach that integrates baseline testing using mock attacks.
- Minimizing the impact of a successful ransomware attack requires detecting it as early in the attack as possible. A Security Information and Event Management (SIEM) system can help an organization to accomplish this. Avertium offers a comprehensive SIEM-based approach that increases the potential for detecting a ransomware infection before it deploys. SIEM provides a holistic overview of a company’s IT environment from a single point of view in terms of its specific security events, empowering teams to detect and analyze unusual behavior.
avertium's recommendations
- It is advisable that you do not open documents from unknown or suspicious sources.
- If you already are a 0patch user, the micro-patch is available on all online 0patch Agents. If you are new to the 0pach platform, you can create a new account here, where you can receive an automatic patch application without rebooting your device.
INDICATORS OF COMPROMISE (IOCS):
At this time, there are no known IoCs associated with the Mark-of-the-web vulnerability. Avertium’s threat hunters remain vigilant in locating IoCs for our customers. Should any be located, Avertium will disclose them as soon as possible. For more information on how Avertium can help protect your organization, please reach out to your Avertium Service Delivery Manager or Account Executive.
SUPPORTING DOCUMENTATION
Exploited Windows zero-day lets JavaScript files bypass security warnings (bleepingcomputer.com)
Mark of the Web Windows Zero-Day Receives Unofficial Patch - Binary Defense