Vovalex Ransomware (TIR-20210207)
Overview of Vovalex
This report is an overview of the new Vovalex ransomware. This malware was discovered by the MalwareHunterTeam and maybe the first known ransomware to be written in the D language. As of now, this malware has been detected being distributed through pirated software that masquerades as legitimate software such as various Windows utilities. The goal of this malware is to encrypt files and demand a ransom from the victim to restore access to the files. This report details the attack, ransomware detection, and mitigation techniques that can be implemented to help protect against the Vovalex ransomware attack.
TIR-20210207 Tactics, Techniques, and Procedures
Vovalex ransomware is a new malware that was recently discovered by the MalwareHunterTeam. The goal of this malware attack is to encrypt files on the victim’s host and demand a ransom for the decryptor. What makes this ransomware attack unique is that it may be the first ransomware written in D Language.
Vovalex is distributed through pirated software such as WinRAR, CCleaner, and uTorrent installers. Once the installer is executed, the ransomware launches the legitimate installer and copies itself to a random file name in the %Temp%folder. Next, the encryption phase begins. Vovalex renames every encrypted file by appending the extension ".vovalex" to each one.
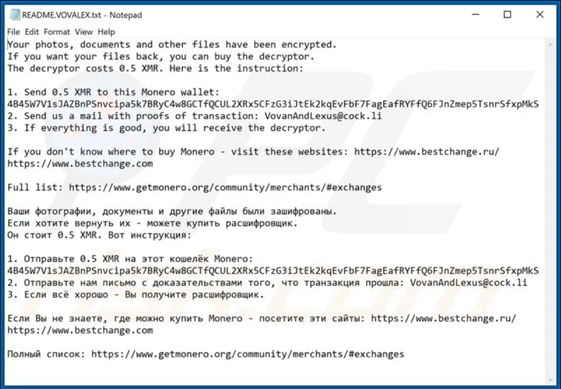
After the files have been encrypted, Vovalex creates a ransom note named README.VOVALEX.txt on the desktop. The note requests 0.5 XMR (Monero) from the victim, which is approximately $69.54, to retrieve a decryptor. The "README.VOVALEX.txt" ransom note also provides the victim with the contact and payment information. This note is written in both English and Russian languages. At the moment, it is unknown if any researchers have discovered the decryption code of this ransomware.
"README.VOVALEX.txt" file:
Business Unit Impact
- Attackers may encrypt data on the victim’s system or on large numbers of systems in a network to interrupt availability to system and network resources.
- Data and sensitive information may be lost or destroyed.
Our Recommendations
- Ensure users are only downloading software from legitimate vendors.
- Ensure backups are stored off the system and are protected from common methods adversaries may use to gain access and destroy the backups to prevent recovery.
- Ensure anti-virus software and associated files are up to date.
- Keep applications and operating systems running at the current released patch level.
- Exercise caution with attachments and links in emails.
IOC List:
- Visit the following sites for a list of file hashes associated with this attack:
Sources
- https://exchange.xforce.ibmcloud.com/collection/New-Ransomware-Vovalex-c5d4edaa8c34931d290840089c925393
- https://www.pcrisk.com/removal-guides/20010-vovalex-ransomware
- https://www.bleepingcomputer.com/news/security/vovalex-is-likely-the-first-ransomware-written-in-d/
- https://otx.alienvault.com/pulse/60155f980befe24ec71060be
Supporting Documentation
- MITRE Mapping(s)
Note: The Avertium Threat Report analyzes one current threat that has been shared by threat intelligence networks across the globe. Used internally by the Avertium CyberOps Team, this report will outline a “top-of-mind” threat and how it ought to be addressed accordingly.
This informed analysis is based on the latest data available.