- WHY AVERTIUM?
-
-
Why Avertium?
Context over chaos. Disconnected technologies, siloed data, and reactive processes can only get you so far. Protecting businesses in today’s threat landscape demands more than a set of security tools – it requires context.
That's where Avertium comes in
-
Considering Microsoft?
Avertium Named Microsoft Security Solutions PartnerAvertium’s managed services for Microsoft Security Solutions is delivered through the company’s premium service: Fusion MXDR. Fusion MXDR includes 24x7 monitoring and management of Defender for Endpoint and Sentinel, threat intelligence, attack surface
monitoring, and vulnerability management for Microsoft Security customers. -
Latest Avertium News
How Gartner's 2024 Cybersecurity Trends Can Guide Your Cyber EffortsGartner has identified its six top cybersecurity trends for the year, and they’re ones that healthcare leaders should consider. Of the six trends, here are the ones that Avertium finds most instructive and beneficial.
-
-
- SOLUTIONS
-
-
Governance, Risk, + Compliance
GRC with context – not complexity. -
Attack Surface Management
No more blind spots, weak links, or fire drills. -
Threat Detection + Response
Detect, adapt, and attack with context. -
Microsoft Security Solutions
End-to-end support from strategy to daily operations to maximize your Microsoft Security.
-
-
- COMPANY
-
-
About Us
Security. It’s in our DNA. It’s elemental, foundational. Something that an always-on, everything’s-IoT-connected world depends on.
Helping mid-to-enterprise organizations protect assets and manage risk is our only business. Our mission is to make our customers’ world a safer place so that they may thrive in an always-on, connected world.
-
Latest Avertium News
How Gartner's 2024 Cybersecurity Trends Can Guide Your Cyber EffortsGartner has identified its six top cybersecurity trends for the year, and they’re ones that healthcare leaders should consider. Of the six trends, here are the ones that Avertium finds most instructive and beneficial.
-
-
- PARTNERS
-
-
Our Partners
Best-in-class technology from our partners... backed by service excellence from Avertium.
-
Partner Opportunity Registration
Interested in becoming a partner?
With Avertium's deal registration, partners can efficiently and confidently connect with Avertium on opportunities to protect your deals.
-
Latest Avertium Resource
Harnessing Copilot for Security: A Strategic Approach to Healthcare Cyber DefenseMicrosoft Copilot for Security analyzes and synthesizes high volumes of security data which can help healthcare cybersecurity teams do more with less.
-
-
- NEWS & RESOURCES
-
-
News & Resources
Dive into our resource hub and explore top
cybersecurity topics along with what we do
and what we can do for you. -
Latest Resource
Harnessing Copilot for Security: A Strategic Approach to Healthcare Cyber DefenseMicrosoft Copilot for Security analyzes and synthesizes high volumes of security data which can help healthcare cybersecurity teams do more with less.
-
-
- CONTACT
Financial Institutions Beware: New PyVil RAT targets you
PyVil Trojan Overview
This threat report is about threat actor Evilnum’s new remote access trojan (RAT) called PyVil and provides actionable intelligence on how to avoid it.
The trojan is built off a new infection chain the threat actor utilizes to propagate malware. The infection chain is very complex and offers a unique method to maintain a fileless presence on the affected host.
The goal of this new infection chain seems to be for financial gain and primarily targets financial institutions.
PyVil RAT Tactics, Techniques, and Procedures
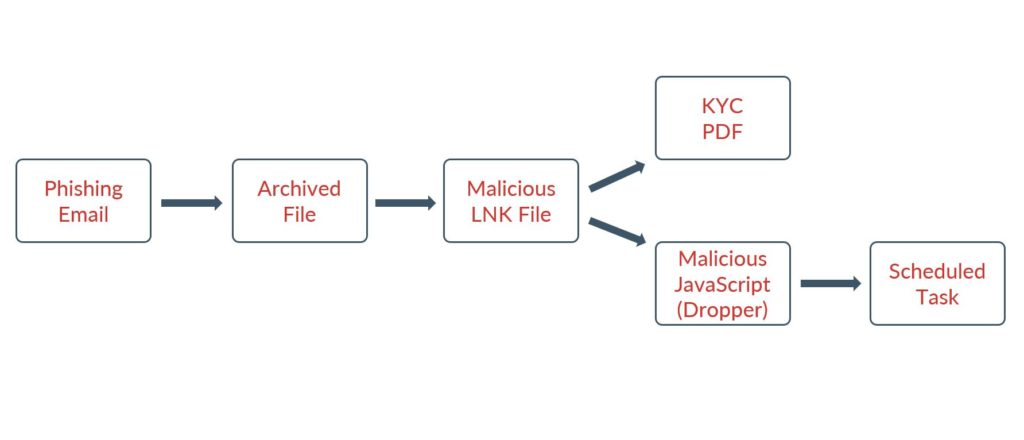
The PyVil RAT starts the infection chain by sending the desired target phishing emails until one gets opened by a user. These emails usually pretend to be utility bills, credit card photos, or driver's license photos. The user will open a zip file attachment that will contain an LNK file which will drop the first payload written in JavaScript.
The early infection process is shown below:
The scheduled task is set up to maintain long-term persistence in the infected device and create a mechanism for pulling down more payloads. The next set of payloads lead to the final remote access trojan being set up on the host which has been written in Python. The bad actor also attempts to dump the existing credentials on the affected host.
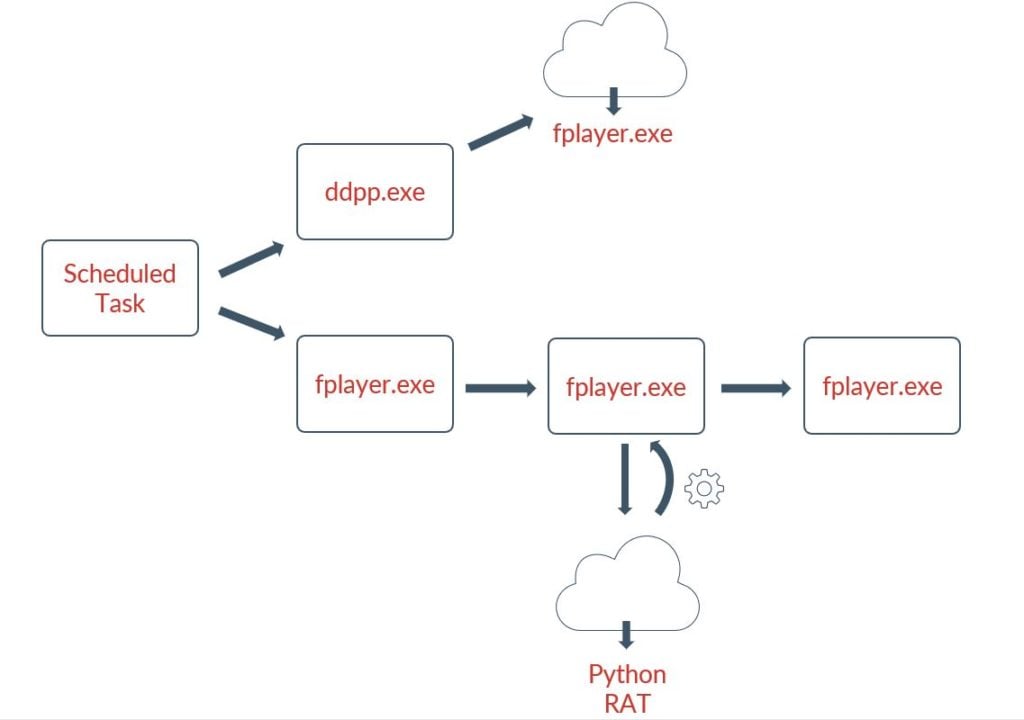
Once the Python-based RAT is installed, it runs the rest of its operations in memory. Communication with the command & control infrastructure uses RC4 encryption using hardcoded keys with Base64 encoding. Information transmitted about the infected machine occurs in JSON.
Related Reading: How to Protect Workers from Increased Phishing Attacks During COVID-19
What This Means to You
- May lead of the loss of sensitive system information and configuration.
- Could result in the loss of credentials for mission-critical applications and services.
- May result in unwanted network activity involving the SHH protocol and web traffic.
- May lead to the propagation of malware on the affected host.
What You Can Do
It is highly encouraged that you perform the following actions to avoid this malware campaign:
- Consider training your users on the dangers of phishing and social engineering.
- Utilize endpoint detection software like Sophos Central or Carbon Black to block unsigned or unwanted executables from running in the environment.
- Add the indicators of compromise to your block list using the link found below.
- Disable to use of the command prompt on user accounts that don’t need it for their job duties.
Sources and Other Helpful Information
MITRE Mappings:
- https://attack.mitre.org/techniques/T1566/002/
- https://attack.mitre.org/techniques/T1053/005/
- https://attack.mitre.org/techniques/T1204/
- https://attack.mitre.org/techniques/T1059/003/
- https://attack.mitre.org/techniques/T1059/007/
- https://attack.mitre.org/techniques/T1056/001/
- https://attack.mitre.org/techniques/T1539/
- https://attack.mitre.org/techniques/T1056/001/
- https://attack.mitre.org/techniques/T1113/
Other useful information:
- https://www.cybereason.com/blog/no-rest-for-the-wicked-evilnum-unleashes-pyvil-rat
- https://www.cybereason.com/hubfs/Evilnum%20IOCs.pdf
Contact us for information about Avertium’s managed security service capabilities.

8 Steps to Take if You've Been Breached
With the prevalence, severity, and sophistication of cybersecurity attacks growing by the day, businesses of all types and sizes are scrambling to protect themselves. This best practices guide takes you through the 8 essential steps to managing a data breach. Download now.
Note: The Avertium Threat Report analyzes one current threat that has been shared by threat intelligence networks across the globe. Used internally by the Avertium CyberOps Team, this report will outline a “top-of-mind” threat and how it ought to be addressed accordingly.
This informed analysis is based on the latest data available.