- WHY AVERTIUM?
-
-
Why Avertium?
Context over chaos. Disconnected technologies, siloed data, and reactive processes can only get you so far. Protecting businesses in today’s threat landscape demands more than a set of security tools – it requires context.
That's where Avertium comes in
-
Considering Microsoft?
Avertium Named Microsoft Security Solutions PartnerAvertium’s managed services for Microsoft Security Solutions is delivered through the company’s premium service: Fusion MXDR. Fusion MXDR includes 24x7 monitoring and management of Defender for Endpoint and Sentinel, threat intelligence, attack surface
monitoring, and vulnerability management for Microsoft Security customers. -
Latest Avertium News
How Gartner's 2024 Cybersecurity Trends Can Guide Your Cyber EffortsGartner has identified its six top cybersecurity trends for the year, and they’re ones that healthcare leaders should consider. Of the six trends, here are the ones that Avertium finds most instructive and beneficial.
-
-
- SOLUTIONS
-
-
Governance, Risk, + Compliance
GRC with context – not complexity. -
Attack Surface Management
No more blind spots, weak links, or fire drills. -
Threat Detection + Response
Detect, adapt, and attack with context. -
Microsoft Security Solutions
End-to-end support from strategy to daily operations to maximize your Microsoft Security.
-
-
- COMPANY
-
-
About Us
Security. It’s in our DNA. It’s elemental, foundational. Something that an always-on, everything’s-IoT-connected world depends on.
Helping mid-to-enterprise organizations protect assets and manage risk is our only business. Our mission is to make our customers’ world a safer place so that they may thrive in an always-on, connected world.
-
Latest Avertium News
How Gartner's 2024 Cybersecurity Trends Can Guide Your Cyber EffortsGartner has identified its six top cybersecurity trends for the year, and they’re ones that healthcare leaders should consider. Of the six trends, here are the ones that Avertium finds most instructive and beneficial.
-
-
- PARTNERS
-
-
Our Partners
Best-in-class technology from our partners... backed by service excellence from Avertium.
-
Partner Opportunity Registration
Interested in becoming a partner?
With Avertium's deal registration, partners can efficiently and confidently connect with Avertium on opportunities to protect your deals.
-
Latest Avertium Resource
Harnessing Copilot for Security: A Strategic Approach to Healthcare Cyber DefenseMicrosoft Copilot for Security analyzes and synthesizes high volumes of security data which can help healthcare cybersecurity teams do more with less.
-
-
- NEWS & RESOURCES
-
-
News & Resources
Dive into our resource hub and explore top
cybersecurity topics along with what we do
and what we can do for you. -
Latest Resource
Harnessing Copilot for Security: A Strategic Approach to Healthcare Cyber DefenseMicrosoft Copilot for Security analyzes and synthesizes high volumes of security data which can help healthcare cybersecurity teams do more with less.
-
-
- CONTACT
Palo Alto PAN-OS Vulnerability with CVSS score of 10 issued
Palo Alto PAN-OS Vulnerability Overview
This threat report is about a newly discovered critical vulnerability in the Palo Alto PAN-OS. The threat has been named CVE-2020-2021 and was published on 06-29-20 by Palo Alto. CVE-2020-2021 is assigned the highest possible CVSS score of 10.
The issue lies within the configuration of SAML authentication and may allow malicious actors access to PAN-OS devices without authentication. Though no POC (proof-of-concept) code is currently available, an exploit of this vulnerability is to be expected in the near future.
Related Reading: We recently covered several critical Palo Alto firewall vulnerabilities and how to remediate them.
CVE-2020-2021 Tactics, Techniques, and Procedures
PAN-OS is affected by this vulnerability if SAML authentication is enabled and the “Validate Identity Provider Certificate” option is not enabled. Some Identity Providers (DUO, Okta, etc.) may have instructions to not enable the “Validate Identity Provider Certificate” due to using self-signed certificates. A bad actor may be able to exploit this misconfiguration to gain unauthorized access as an administrator. For a bad actor to exploit this vulnerability they must have internal network access to the device, or it must be publicly exposed on the internet.
This Palo Alto Pan-OS vulnerability affects the following resources and versions:
- GlobalProtect Gateway
- GlobalProtect Portal
- GlobalProtect Clientless VPN
- Authentication and Captive Portal
- PAN-OS next-generation firewalls
- Panorama web interfaces
- Prisma Access
- PAN-OS 9.1 versions earlier than PAN-OS 9.1.3
- PAN-OS 9.0 versions earlier than PAN-OS 9.0.9
- PAN-OS 8.1 versions earlier than PAN-OS 8.1.15
- All versions of PAN-OS 8.0
What the Palo Alto Pan-Os Vulnerability Means to You
- Vulnerabilities of this nature have a very high likelihood of being exploited on a large scale by well-known threat actors.
- May result in unauthorized access and changes to PAN-OS devices by bad actors.
- May result in compromise of VPN devices.
- May provide bad actors a point of initial access to laterally move within your network.
What You Can Do About CVE-2020-2021
Palo Alto provides the below infographic for checking your systems:
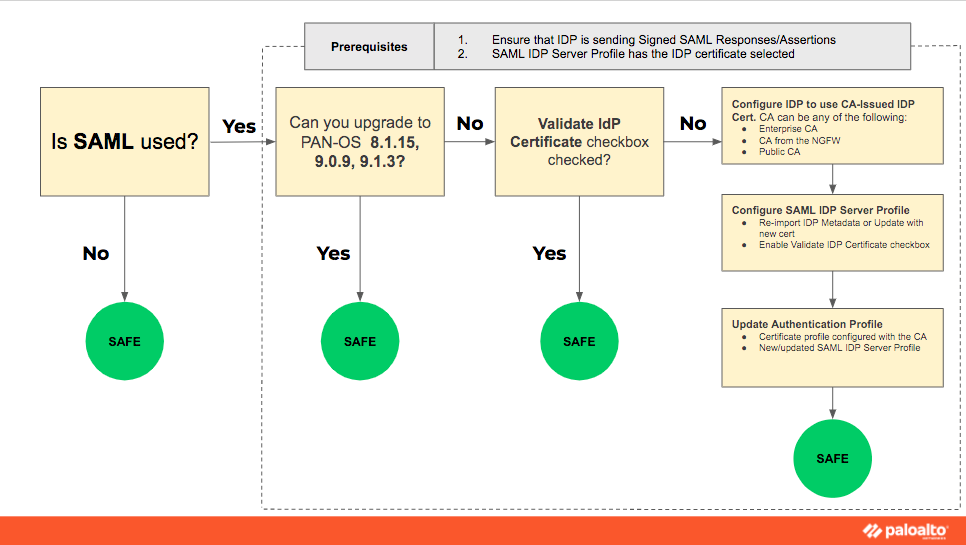
The risk from this vulnerability can be fully avoided if SAML authentication is not enabled on your PAN-OS device. SAML authentication should be disabled by default. If you use SAML authentication, we recommend the patches be applied either directly through the device or through the Palo Alto support portal.
Patches for CVE-2020-2021
- Update versions of PAN-OS 9.1 to PAN-OS 9.1.3 or greater.
- Update versions of PAN-OS 9.0 to PAN-OS 9.0.9 or greater.
- Update versions of PAN-OS 8.1 to PAN-OS 8.1.15 or greater.
- Versions of PAN-OS 8.0 will likely need to be upgraded to PAN-OS 9.0 before upgrading to a non-vulnerable version. The upgrade path is detailed here: https://knowledgebase.paloaltonetworks.com/KCSArticleDetail?id=kA10g000000PMX0CAO
Sources and Supporting Documentation
- https://security.paloaltonetworks.com/CVE-2020-2021
- https://knowledgebase.paloaltonetworks.com/KCSArticleDetail?id=kA14u0000008UXK
MITRE Mapping(s)
- Initial Access: https://attack.mitre.org/tactics/TA0001/
- External Remote Services: https://attack.mitre.org/techniques/T1133/
Note: The Avertium Threat Report analyzes one current threat that has been shared by threat intelligence networks across the globe. Used internally by the Avertium CyberOps Team, this report will outline a “top-of-mind” threat and how it ought to be addressed accordingly.
This informed analysis is based on the latest data available.
Contact us for more information about Avertium’s managed security service capabilities.
Deciding between running an in-house SOC vs. using managed security services (MSS) to add more rigor, more relevance, and more responsiveness to your cybersecurity program? Compare the two options. Download the e-book!