- WHY AVERTIUM?
-
-
Why Avertium?
Context over chaos. Disconnected technologies, siloed data, and reactive processes can only get you so far. Protecting businesses in today’s threat landscape demands more than a set of security tools – it requires context.
That's where Avertium comes in
-
Considering Microsoft?
Avertium Named Microsoft Security Solutions PartnerAvertium’s managed services for Microsoft Security Solutions is delivered through the company’s premium service: Fusion MXDR. Fusion MXDR includes 24x7 monitoring and management of Defender for Endpoint and Sentinel, threat intelligence, attack surface
monitoring, and vulnerability management for Microsoft Security customers. -
Latest Avertium News
How Gartner's 2024 Cybersecurity Trends Can Guide Your Cyber EffortsGartner has identified its six top cybersecurity trends for the year, and they’re ones that healthcare leaders should consider. Of the six trends, here are the ones that Avertium finds most instructive and beneficial.
-
-
- SOLUTIONS
-
-
Governance, Risk, + Compliance
GRC with context – not complexity. -
Attack Surface Management
No more blind spots, weak links, or fire drills. -
Threat Detection + Response
Detect, adapt, and attack with context. -
Microsoft Security Solutions
End-to-end support from strategy to daily operations to maximize your Microsoft Security.
-
-
- COMPANY
-
-
About Us
Security. It’s in our DNA. It’s elemental, foundational. Something that an always-on, everything’s-IoT-connected world depends on.
Helping mid-to-enterprise organizations protect assets and manage risk is our only business. Our mission is to make our customers’ world a safer place so that they may thrive in an always-on, connected world.
-
Latest Avertium News
How Gartner's 2024 Cybersecurity Trends Can Guide Your Cyber EffortsGartner has identified its six top cybersecurity trends for the year, and they’re ones that healthcare leaders should consider. Of the six trends, here are the ones that Avertium finds most instructive and beneficial.
-
-
- PARTNERS
-
-
Our Partners
Best-in-class technology from our partners... backed by service excellence from Avertium.
-
Partner Opportunity Registration
Interested in becoming a partner?
With Avertium's deal registration, partners can efficiently and confidently connect with Avertium on opportunities to protect your deals.
-
Latest Avertium Resource
Harnessing Copilot for Security: A Strategic Approach to Healthcare Cyber DefenseMicrosoft Copilot for Security analyzes and synthesizes high volumes of security data which can help healthcare cybersecurity teams do more with less.
-
-
- NEWS & RESOURCES
-
-
News & Resources
Dive into our resource hub and explore top
cybersecurity topics along with what we do
and what we can do for you. -
Latest Resource
Harnessing Copilot for Security: A Strategic Approach to Healthcare Cyber DefenseMicrosoft Copilot for Security analyzes and synthesizes high volumes of security data which can help healthcare cybersecurity teams do more with less.
-
-
- CONTACT
APT38 Threat Actor Profile
Executive Summary
This report is a threat actor profile on APT38 and the various operations the group engages in. APT38 is a nation-state level threat group associated with the North Korean regime whose sole purpose is to collect sensitive financial data. The financial data is often collected from banks and other institutions to capture hard currency, such as USD, for the Kim regime.
APT38 Tactics, Techniques, and Procedures
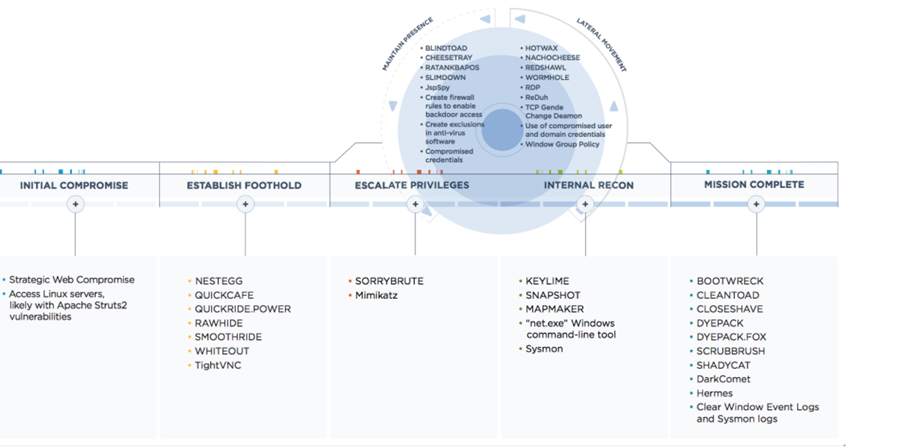
The threat actor has a specific lifecycle that most of its campaigns typically fall under, with some variance for specialized environments. The bad actor starts by exploiting vulnerable public-facing infrastructure, such as web servers with an unpatched Apache Struts deployment. They use a mix of custom and common security assessment tools to perform lateral movement into the internal network. APT38 then uses customized malware to maintain persistence on a machine where they will launch privilege escalation attacks (using a tool like Mimikatz). As they assess the network via internal reconnaissance, the bad actor will be looking for the SWIFT transaction system. Once the SWIFT transaction system has been identified, the threat actor will look for weaknesses by studying how the system is monitored and configured. The ideal weakness will allow them to install a backdoor on both the SWIFT transaction system and the surrounding monitoring devices.
Please see the graphic below for an overview of the attacker’s lifecycle:
Once the bad actor installs a backdoor on any system related to transaction processing, they’ll start to move funds to illicit accounts over an extended period. When transfers are complete, APT38 will begin scrubbing the environment of evidence. It will start with the deletion of Windows event logs, deletion of malware artifacts, memory scrubbing, and much more!
Strategic Impact of APT38
- May lead to the loss of sensitive user credentials and the compromise of high-value user accounts.
- Could result in the loss of monetary funds via illicit transactions using your processing infrastructure.
- May lead to regulatory fines if a successful compromise occurs, such as GDPR or PCI DSS penalties. This will be the case if gross negligence is discovered.
Our Recommendations
It is highly encouraged that you patch your public-facing infrastructure if the impact is minimal to your business operations. Consider using the Mimikatz defense guide linked below to improve your defensive posture.
Sources
- APT38, NICKEL GLADSTONE, BeagleBoyz, Bluenoroff, Stardust Chollima, Group G0082 – Mitre ATT&CK (October 2021)
Supporting Documentation
- APT Campaign Collection – GitHub
- APT38: Details on New North Korean Regime-Backed Threat Group – Mandiant (October 2018)
- Mimikatz Defense Guide (Mitigations against Mimikatz Style Attacks) – Internet Storm Center, Rob VandenBrink (February 2019)
MITRE Mapping(s)
- DarkComet, Software S0334 – Mitre ATT&CK (March 2020)
- Mimikatz, Software S0002 – Mitre ATT&CK (May 2021)
- Net, Software S0039 – Mitre ATT&CK (October 2021)
Note: The Avertium Threat Report analyzes one current threat that has been shared by threat intelligence networks across the globe. Used internally by the Avertium CyberOps Team, this report will outline a “top-of-mind” threat and how it ought to be addressed accordingly.
This informed analysis is based on the latest data available.